Latest Two-factor authentication vulnerabilities review
According to information regards the latest security incidents with LastPass, Cisco, Uber, and Okta, adversaries exploited two-factor authentication procedures to disable or bypass access control. Such techniques as MFA Bombing, Fishing, MFA fatigue, and 2FA Men-in-the-Middle (MiTM) attacks were used to mislead end-user, steal plain text passwords and perform MiTM on two-factor authentication. The user-friendly feature “Allow authentication request” was misused as a tool. In all cases, adversaries were able to bypass two-factor authentication by either disabling it on target accounts, stealing MFA secrets, or adding a new MFA profile.Social Engineering (SE)
In the case of Uber, the attacker first somehow discovered the employee’s WhatsApp number, started a Messaging chat, and send an URL to the victim with the fake Uber site login page. After that intruder applied SE to convince the legitimate user to enter login credentials on a spoofed Uber login page.MFA bombing by push notifications
After successfully stealing the user login and password, the attacker initiated an MFA bombing/MiTM attack by login into a legitimate Uber login page multiple times, generating a storm of push notifications “Accept login request” to the employee’s smartphone. At some moment the user confirmed the request thus allowing the attacker to access the system.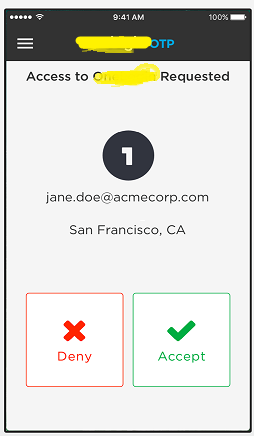
MFA provider re-enrolling
In the case of the Microsoft breach, hackers re-enrolled smartphone-based MFA (push tokens) on a new device by accessing the Okta MFA provider account (or partial MFA vendor infrastructure takeover) and then performing login into the target user’s MS accounts by using MFA duplicates.How to improve your MFA / 2FA control?
Here are a few pieces of advice on how to check your current MFA implementation for improvements:- Train your employees on how to report/act when MFA access requests on the smartphone appeared at Inappropriate times. After training, perform field tests to generate inappropriate MFA requests to ensure proper reflections by the end user.
- Check if your employees know about a decent and friendly way (Social Re-Engineering?) to verify via phone if they really speak with somebody pretending to be a ‘support desk representative’ from your company.
- Monitor your system’s remote access for inappropriate/suspicious/abnormal activity, for example – out-of-work login time, MFA failure, or too long MFA approval time.
- Continue updating your MFA toolset by employing new MFA technologies like U2F FIDO, FIDO2, and WebAuthn in parallel with the current MFA.
- Check if your MFA vendor/solution has new features to filter access by IP or MFA device. Check if the MFA solution logs MFA activities parameters.
- Use gamification within your IT team to simulate or imagine how MFA re-enrollment, misuse, and bypass may happen in your organization.
What about Rohos Logon Key?
Rohos Logon Key adds strong two-factor authentication control for Windows Remote Desktop access. Rohos allows the implementation and adopts multi-factor authentication into business processes with minimal side effects. In Rohos we always experiment with new features.- You may employ different MFA methods: password, PIN code, Smartphone or strong authentication devices like FIDO2 U2F key, YubiKey, Google Authenticator One-Time password codes, USB iKey tokens, or RFID cards per different user groups depending on requirements or technical skills.
- It is possible to apply MFA by IP filter.
- It is possible to use MFA bypass control – lock the desktop immediately when MFA was not used for the login session.
- Rohos log all type of MFA events: Login session time, MFA prompt time, and successful MFA duration time for each user.
- Rohos for Android/iOS app does not use Push notifications ‘Approve access request’. With the Rohos MFA app – Notification bombing is not possible.
- Rohos allows the addition of more MFA redundancy by setting up FIDO2 physical key and Smartphone app for the specific user account. The MFA diversity can be used to distinguish between logins of legitimate user MFA or stolen/ re-enrolled MFA.
October 2nd, 2022 in
Lösungen
